Shellcode Exploit . Your visual guide for crafting and understanding shellcode. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through direct submissions, mailing. Web shellcode is a set of instructions that executes a command in software to take control of or exploit a. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through. Web examples of shellcode attacks are diverse and often tailored to exploit specific vulnerabilities. Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. Web gdb, assembly and disassembly. In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Ideal for malware, and exploit. One common type is the.
from howtofix.guide
In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Ideal for malware, and exploit. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through direct submissions, mailing. Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. Web shellcode is a set of instructions that executes a command in software to take control of or exploit a. Web gdb, assembly and disassembly. One common type is the. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through. Your visual guide for crafting and understanding shellcode. Web examples of shellcode attacks are diverse and often tailored to exploit specific vulnerabilities.
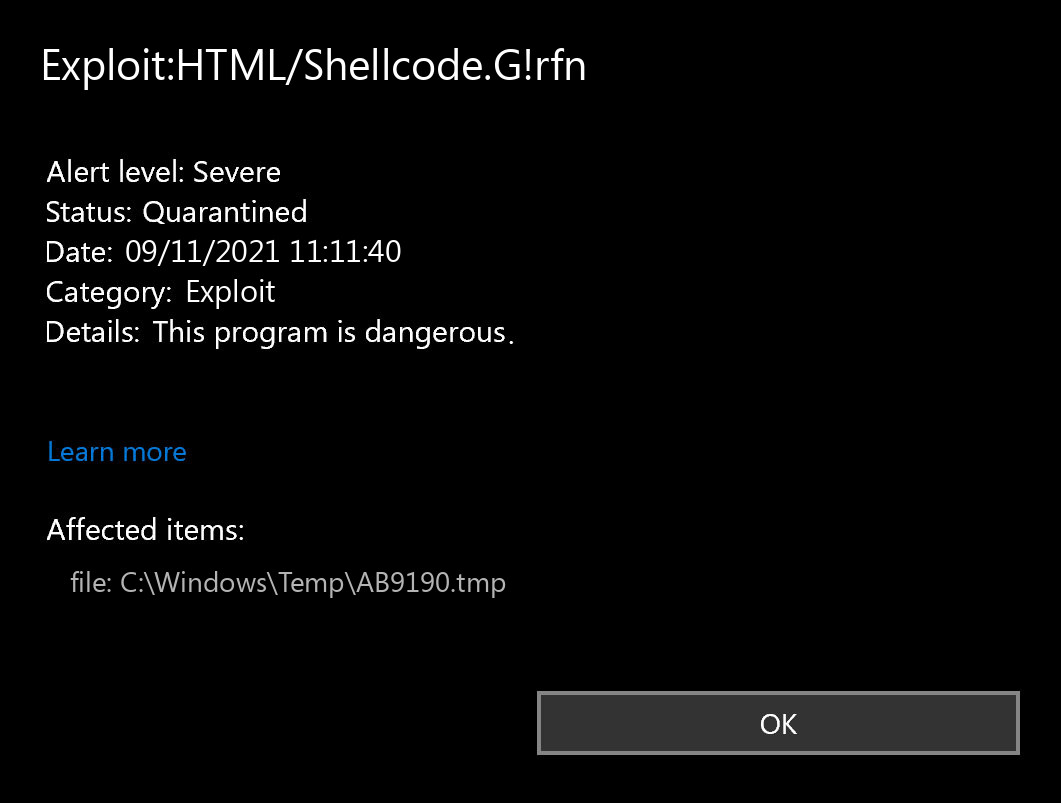
ExploitHTML/Shellcode.G!rfn (Shellcode Exploit) — Virus Removal Guide
Shellcode Exploit In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Your visual guide for crafting and understanding shellcode. Ideal for malware, and exploit. One common type is the. In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through direct submissions, mailing. Web gdb, assembly and disassembly. Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through. Web shellcode is a set of instructions that executes a command in software to take control of or exploit a. Web examples of shellcode attacks are diverse and often tailored to exploit specific vulnerabilities.
From howtofix.guide
ExploitHTML/Shellcode.G!rfn (Shellcode Exploit) — Virus Removal Guide Shellcode Exploit Ideal for malware, and exploit. Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. One common type is the. Web examples of shellcode attacks are diverse and often tailored to exploit specific vulnerabilities. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered. Shellcode Exploit.
From www.youtube.com
Exploit Shellcode Geliştirme Bölüm7 Shellcode'un Geliştirilmesi Shellcode Exploit Your visual guide for crafting and understanding shellcode. In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Ideal for malware, and exploit. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through. Web gdb, assembly and disassembly. Web its aim is. Shellcode Exploit.
From www.shelliscoming.com
Shell is coming OneWay Shellcode for firewall evasion using Out Shellcode Exploit Web gdb, assembly and disassembly. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through direct submissions, mailing. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through. Web the term “shellcode” was historically used to describe code executed by a target program due. Shellcode Exploit.
From www.sentinelone.com
How Hackers Use Shellcode? An Easy Guide 101 Shellcode Exploit Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through direct submissions, mailing. Web examples of shellcode attacks are diverse and often tailored to exploit specific vulnerabilities. Web shellcode is a set of. Shellcode Exploit.
From howtofix.guide
ExploitJava/Shellcode!MTB — Virus Removal Guide Shellcode Exploit Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. Web shellcode is a set of instructions that executes a command in software to take control of or exploit a. One common type is the. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers. Shellcode Exploit.
From howtofix.guide
ExploitHTML/Shellcode!MSR — Virus Removal Guide Shellcode Exploit Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through direct submissions, mailing. Your visual guide for crafting and understanding shellcode. In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Web the term “shellcode” was historically used to describe code executed. Shellcode Exploit.
From www.youtube.com
Exploit Shellcode Geliştirme Bölüm8 Shellcode Problemleri Kötü Shellcode Exploit Web gdb, assembly and disassembly. Your visual guide for crafting and understanding shellcode. Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. One common type is the. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through. Web shellcode is a set. Shellcode Exploit.
From www.youtube.com
Exploit Shellcode Geliştirme Bölüm3 Standart Bir Uygulama YouTube Shellcode Exploit Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through direct submissions, mailing. Web shellcode is a set of instructions that executes a command in software to take control of or exploit a. Web. Shellcode Exploit.
From howtofix.guide
ExploitWin32/ShellCode!ml — Virus Removal Guide Shellcode Exploit One common type is the. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through direct submissions, mailing. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through. Your visual guide for crafting and understanding shellcode. Web shellcode is a set of instructions that. Shellcode Exploit.
From xavibel.com
Shellcode Windows/x86 Create Administrator User Dynamic PEB & EDT Shellcode Exploit Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. One common type is the. Web examples of shellcode attacks are diverse and often tailored to exploit specific vulnerabilities. Web shellcode is a set of instructions that executes a command in software to take control of or exploit a. Web gdb,. Shellcode Exploit.
From www.youtube.com
Windows Exploit Development Shellcode YouTube Shellcode Exploit Web gdb, assembly and disassembly. In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Web shellcode is a set of instructions that executes a command in software to take control of or exploit a. One common type is the. Your visual guide for crafting and understanding shellcode. Ideal for. Shellcode Exploit.
From www.youtube.com
PIROP exploit injecting shellcode in Asterisk (EuroSP '18) YouTube Shellcode Exploit Ideal for malware, and exploit. Web gdb, assembly and disassembly. Web shellcode is a set of instructions that executes a command in software to take control of or exploit a. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through direct submissions, mailing. In this article we will details how to exploit. Shellcode Exploit.
From www.securitysift.com
Windows Exploit Development Part 4 Locating Shellcode With Jumps Shellcode Exploit Web gdb, assembly and disassembly. One common type is the. In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through. Web the term “shellcode” was historically used to describe code executed by. Shellcode Exploit.
From howtofix.guide
ExploitJS/ShellCode.BH — Virus Removal Guide Shellcode Exploit In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. Ideal for malware, and exploit. One common type is the. Your visual guide for crafting and understanding shellcode. Web gdb, assembly. Shellcode Exploit.
From www.youtube.com
Win32 Exploit Development 17 Generating Shellcode with Mfsvenom YouTube Shellcode Exploit Web shellcode is a set of instructions that executes a command in software to take control of or exploit a. Ideal for malware, and exploit. Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. Your visual guide for crafting and understanding shellcode. One common type is the. Web its aim. Shellcode Exploit.
From www.youtube.com
How to Remove ExploitWin32/ShellCode!rfn? [ Easy Tutorial ] YouTube Shellcode Exploit Web the term “shellcode” was historically used to describe code executed by a target program due to a vulnerability. In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Web gdb, assembly and disassembly. Web examples of shellcode attacks are diverse and often tailored to exploit specific vulnerabilities. Web its. Shellcode Exploit.
From www.youtube.com
Exploits, Payloads e Shellcode. O que você precisa saber YouTube Shellcode Exploit One common type is the. Web gdb, assembly and disassembly. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through. Your visual guide for crafting and understanding shellcode. Web its aim is to serve as the most comprehensive collection of exploits, shellcode and papers gathered through direct submissions, mailing. In this article. Shellcode Exploit.
From www.sentinelone.com
How Hackers Use Shellcode? An Easy Guide 101 Shellcode Exploit In this article we will details how to exploit a buffer overflow in order to achieve remote code execution via. Your visual guide for crafting and understanding shellcode. Web examples of shellcode attacks are diverse and often tailored to exploit specific vulnerabilities. Web shellcode is a set of instructions that executes a command in software to take control of or. Shellcode Exploit.